At NFT Droppers, we provide the latest crypto news, in-depth project information, and comprehensive market insights. Launched in 2022, our platform covers new token launches, market trends, and detailed reviews of crypto and NFT projects. We offer reliable ratings based on 70+ evaluation factors, including tokenomics, roadmaps, and team authenticity. Whether you’re an investor or a crypto enthusiast, NFT Droppers keeps you informed with accurate, up-to-date information and expert analysis.
How To Secure Your Cryptocurrency Investments?

Table of Contents
Investing in cryptocurrencies can be both thrilling and rewarding. However, it also comes with inherent risks due to the decentralized nature of blockchain technology. The absence of a central authority makes it imperative for investors to take extra precautions to secure their cryptocurrency holdings. This comprehensive guide will explore various strategies to fortify and protect your crypto investments from potential threats.
Choose Trusted and Secure Wallets
The foundation of secure cryptocurrency investments lies in selecting suitable wallets. There are two primary types of wallets: hot wallets and cold wallets. Hot wallets are connected to the internet and are ideal for frequent transactions, while cold wallets are offline and provide enhanced security.
Hardware wallets, such as cold wallets, are widely regarded as the most secure option. These physical devices store your private keys offline, mitigating the risk of hacking or phishing attacks. Leading hardware wallets like Ledger and Trezor offer an added layer of protection against unauthorized access and are recommended for long-term cryptocurrency storage.
Utilize Strong Authentication Methods
An essential step in securing your cryptocurrency investments is implementing robust authentication methods. Besides creating a strong and unique password, consider enabling two-factor authentication (2FA). 2FA requires users to provide a second piece of information, typically a one-time code sent to their mobile device, making it significantly harder for hackers to access their accounts.
Additionally, consider utilizing biometric authentication methods, such as fingerprint or facial recognition, if your wallet or exchange platform supports them. These measures enhance security by ensuring that only you can access your accounts.
Keep Software and Devices Updated
Regularly updating your wallet software and devices is crucial to maintaining their security. Software developers continuously release updates to address vulnerabilities and enhance the safety of their products. Ignoring these updates leaves your wallet susceptible to potential exploits and attacks.
Similarly, keep your computer, smartphone, and other devices up to date with the latest security patches. Outdated software may have known vulnerabilities that hackers can exploit to gain unauthorized access to your devices or accounts.
Be Cautious of Phishing Attempts
Phishing attacks are a common tactic cybercriminals use to steal sensitive information, such as login credentials and private keys. These attacks often involve fraudulent emails, websites, or messages that deceive users into disclosing their confidential data.
To protect yourself from phishing attempts, always double-check the authenticity of the websites you visit or the emails you receive. Avoid clicking on suspicious links, and never provide your private keys or login credentials unless you are particular about the request’s legitimacy.
Diversify Your Investments
Diversification is a fundamental principle of investing and holds for cryptocurrencies. Spreading your investments across different cryptocurrencies reduces the risk of a single asset’s poor performance affecting your entire portfolio.
Furthermore, consider diversifying across various types of cryptocurrencies, including established ones like Bitcoin and Ethereum, as well as promising altcoins. Conduct thorough research and due diligence before adding any new cryptocurrency to your portfolio.
Use Decentralized Exchanges (DEXs)
Centralized exchanges are popular targets for hackers due to the vast amounts of digital assets they hold. In contrast, decentralized exchanges (DEXs) operate on a peer-to-peer basis, enabling users to retain control of their funds throughout the trading process.
DEXs eliminate the need to deposit funds into a centralized entity, reducing the risk of exchange hacks. As with any exchange, however, exercise caution, and research the reputation and security measures of the DEX before trading on platforms like Immediate Connect.
Secure Your Internet Connection
Since cryptocurrencies are digital assets, most of their management and transactions occur online. Therefore, securing your internet connection is of utmost importance. Always connect to secure and trusted networks when accessing your wallets or exchange accounts.
Avoid using public Wi-Fi networks, as they are often vulnerable to attacks. Instead, rely on your secure home network or a trusted mobile hotspot. Using a Virtual Private Network (VPN) can also add an extra layer of security by encrypting your data and protecting it from potential eavesdropping.
Many cryptocurrency wallets and exchange platforms offer transaction alert features that notify you whenever a transaction occurs on your account. By enabling these alerts, you will be immediately informed of any unauthorized activity, allowing you to take swift action in case of a security breach.
Backup Your Wallets Regularly
Regardless of the type of wallet you choose, it is essential to regularly back up your wallet data. In case of hardware wallet damage, loss, or theft, having a backup will allow you to restore your funds and access your cryptocurrencies from a new device.
When creating backups, store the files securely in offline locations, such as encrypted USB drives or hardware devices designed explicitly for this purpose. Keep multiple copies of your backup in different physical areas to ensure redundancy and protection against disasters like fires or floods.
Use Multi-Signature Wallets
Multi-signature wallets, or “multi-sig” wallets, add more security to your cryptocurrency holdings. These wallets require multiple private keys to authorize transactions, reducing the risk of unauthorized access even if one of the private keys is compromised.
For example, a 2-of-3 multi-sig wallet would require two out of three private keys to sign a transaction. This setup is handy for businesses or families managing shared funds, as it ensures that no single person can initiate transactions without the approval of others.
Employ Cold Storage for Long-Term Holdings
While hot wallets are convenient for frequent transactions, they are more susceptible to online attacks. For long-term cryptocurrency holdings, consider utilizing cold storage solutions like paper or hardware wallets.
Paper wallets involve printing your private keys and public addresses on physical paper, entirely offline. Since there’s no digital connection, this method is highly secure from online threats. However, store the paper wallet in a safe and protected environment to prevent physical damage or loss.
Be Cautious of Social Engineering Attacks
Social engineering attacks rely on psychological manipulation rather than technical exploits to trick individuals into revealing sensitive information. Scammers may impersonate customer support representatives or cryptocurrency experts to gain your trust and access your accounts.
Always verify the identity of anyone contacting you regarding your crypto investments, especially if they request sensitive information. Legitimate organizations will never ask for your private keys or passwords.
Educate Yourself and Stay Informed
Knowledge is a powerful tool in the world of cryptocurrencies. Stay informed about security threats, hacking techniques, and best practices for securing your digital assets. Regularly educate yourself on cryptocurrency through reputable sources, online forums, and community discussions.
Follow updates from your wallet providers and exchange platforms, which often communicate important security-related information and software updates.
Consider Using Hardware Security Modules (HSMs)
Hardware Security Modules (HSMs) are physical devices designed to generate, store, and manage cryptographic keys securely. They provide an added layer of protection against key theft and unauthorized access to critical information.
HSMs are commonly used by enterprises and institutions to protect large sums of digital assets. While they may not be practical for individual investors with smaller holdings, it’s worth considering for high-net-worth investors or businesses involved in cryptocurrency.
Regularly Review and Audit Your Accounts
Monitor your cryptocurrency accounts, wallets, and exchange platforms for suspicious activities or transactions. Regularly review your account history to ensure that all actions were initiated by you or authorized users.
If you notice any unusual activity, immediately change your passwords, deactivate compromised accounts, and contact customer support or relevant authorities if necessary.
Conclusion
Securing your cryptocurrency investments is an ongoing process that requires a combination of technology, awareness, and best practices. You can protect your digital assets from potential threats by employing trusted wallets, enabling robust authentication methods, and diversifying your holdings. Regularly updating your software, backing up your wallets, and being cautious of social engineering attacks are essential to maintaining security.
Remember, investing in cryptocurrencies involves inherent risks, but taking proactive measures to safeguard your investments will significantly reduce vulnerabilities and enhance the overall safety of your crypto journey. Stay informed, educate yourself about potential threats, and remain vigilant in managing your cryptocurrency holdings. With suitable precautions, you can confidently navigate the world of cryptocurrencies and protect your investments for the long term.

Disclaimer: The information presented here may express the authors personal views and is based on prevailing market conditions. Please perform your own due diligence before investing in cryptocurrencies. Neither the author nor the publication holds responsibility for any financial losses sustained.
Top Crypto Presales
 Ionix Chain $IONX
Ionix Chain $IONXBEST CRYPTO CASINO
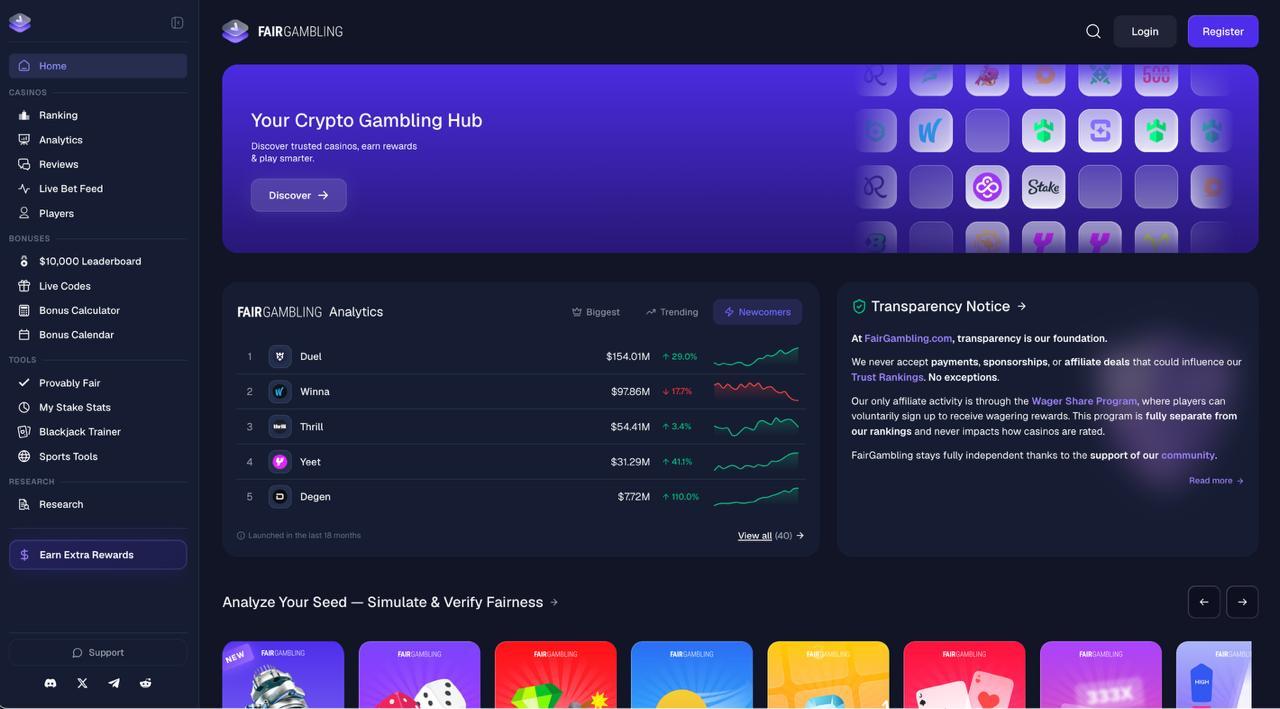
TOP EXCHANGES
CRYPTO PAYMENT GATEWAY
 Crypto Cloud
Crypto CloudBEST HARDWARE WALLET
 Tangem
Tangem Gamdom
Gamdom Stake.com
Stake.com Coins.Game Casino
Coins.Game Casino